
Homeland Security warns of ‘BrickerBot’ malware that destroys unsecured IoT devices
Reminiscent of the Mirai botnet that brought down large swathes of the US internet last year, this new malware targets poorly-secured Internet of Things devices and renders them useless.
By Zack Whittaker for Zero Day | April 19, 2017 | Topic: Security
A new kind of attack is targeting unsecured Internet of Things devices by scrambling their code and rendering them useless.
Security firm Radware first spotted the newly-found “BrickerBot” malware last month after it started hitting its own honeypots, logging hundreds of infection attempts over a few days. When the malware connects to a device with their default usernames and passwords — often easily found on the internet — the malware corrupts the device’s storage, leading to a state of permanent denial-of-service (PDoS) attack, known as “bricking.”
In other words, this attack, “damages a system so badly that it requires replacement or reinstallation of hardware,” said Radware.
It’s a novel take on an ongoing security problem with Internet of Things devices: botnets controlled by hackers, like the Mirai malware, typically infect unsecured devices that are enlisted as part of wider bandwidth-stealing attacks to bring down websites and services by overwhelming them with internet traffic.
Like the Mirai botnet, most famous for bringing down wide swathes of the US internet last year in a massive distributed denial-of-service (DDoS) attack, the BrickerBot also uses “the same exploit vector” by brute-forcing telnet accounts with lists of available usernames and passwords.
Radware doesn’t have a list of internet-connected devices, like webcams, toys, and even smart bulbs, at risk of being attacked, but pointed to several kinds of Linux-based devices that run the BusyBox toolkit that have their telnet port open, and are exposed publicly on the internet.
The researchers say that the attackers also have an affinity for targeting devices on Ubiquiti networks, which have been targeted by attackers before.
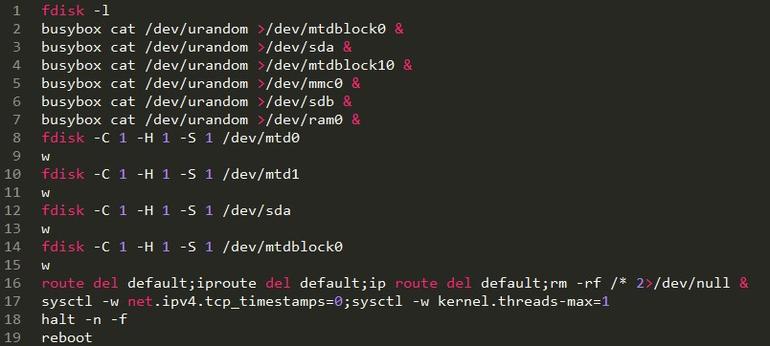
Once inside, the malware runs a sequence of commands, which “try to remove the default gateway, wipe the device through rm -rf /* and disable TCP timestamps as well as limiting the max number of kernel threads to one,” which would scramble the device’s memory.
The researchers also say that the malware adds extra commands “to flush all iptables firewall and NAT rules and add a rule to drop all outgoing packets,” effectively wiping any trace of its infection.
“Unfortunately, even after performing the factory reset, the camera was not recovered and hence it was effectively bricked,” said Radware.
And, because the device-bricking bot conceals its location through the Tor anonymity network, there’s no way to know where the attack came from, the researchers said.
The emergence of BrickerBot has prompted Homeland Security’s Cyber Emergency Response Team (CERT) to issue an updated warning, noting that “no information is available at this time about the type and number of devices used in performing these attacks.”
“Control systems often have Internet accessible devices installed without the owner’s knowledge, putting those systems at increased risk of attack,” said the advisory.
The researchers say that a device search could point to at least 21 million devices at risk, but the motivations for this new attack aren’t known.
Homeland Security suggests changing a device’s default credentials and disabling telnet.
This article was published at zdnet.com
No Comments




